The data was cached even though the information was only entered on secure sites that should not have allowed for the information to be skimmed and collected. When Chrome was first released we noticed unusual behavior in that the browser consistently wrote and read data from the System Volume Information file. This is not a normal file for a web browser to talk to much less write data to. Shortly after we discovered this a flaw was revealed that allowed a remote user to view stored web pages with all information visible including bank information. This data was present even when using the private browsing feature.
Now that we have more information we can see that Google is collecting a lot more data than they should. What is being done with this data we do not know, but Identity Finders did discover that the cache where all of this sensitive data is stored is unprotected and open to being read by anyone that can access the file system. This includes remote access, physical access or through the use of code that parses the file and transmits data to a central server.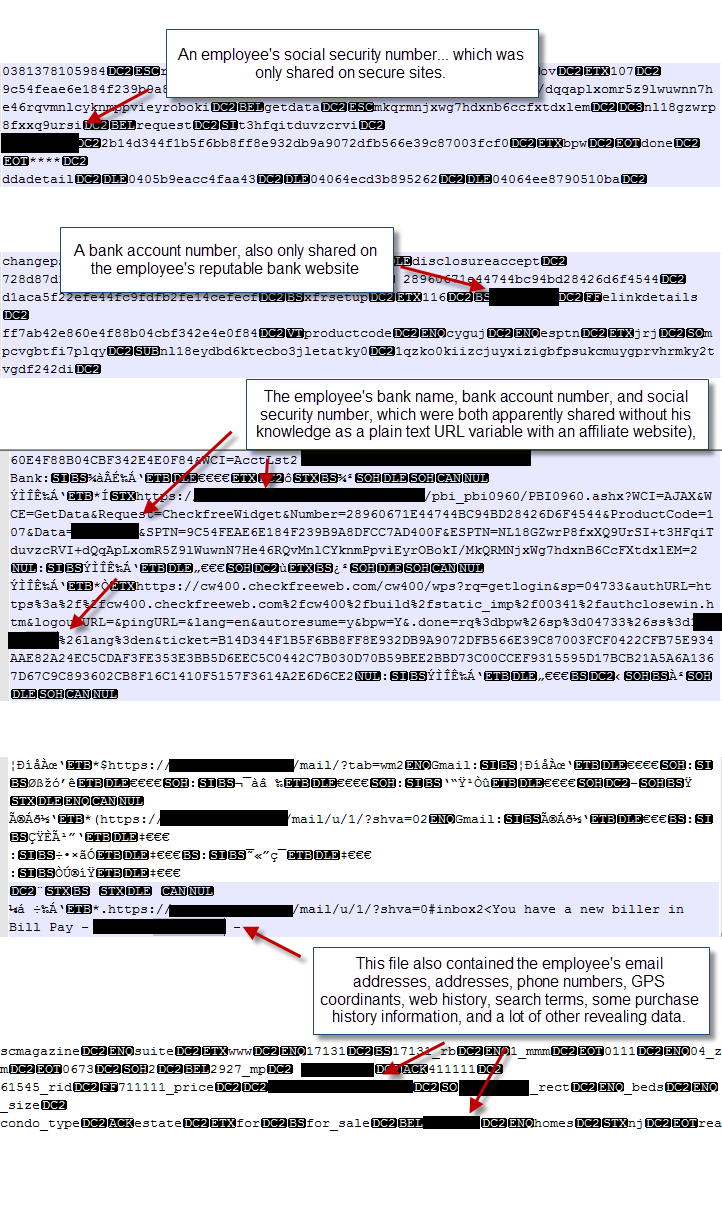
This last bit of information is even more concerning as many malware programs look for this type of unprotected cache. The more paranoid could also see it as an intentional weakness put in for use by the NSA. Considering the way the files are open and how much data they collect it could be a treasure trove of information for an NSA sweep. We already know that the NSA does use Malware in their data collection effort and Chrome’s browsing and history caches seems almost tailor made of that type of work.
Identity Finders admits that this vulnerability has always been suspected, but that they are the first to actually show a real-world example of this flaw. They have notified Google and we hope that Google will actually address this flaw very quickly. For now we suggest that you always clear your history and cache when you are done browsing. In addition you might want to manually delete any files in the %localappdata%\Google\Chrome\User Data\Default\ folder. The SQLite databases in question are History Provider Cache, Web Data and History. Identity Finders also admits that other browsers potentially have a similar flaw, but that Chrome is the first one they have tested with the new methods.
Tell us what you think in our Forum

