Displaying items by tag: Certificate Authority
CA/Browser Forum Changes Will Break Many Existing Networks
 |
We have a new winner of the “what were they thinking award” the CA/Browser Forum have won this one by changing the way that certificates are issued. Normally such changes are not intrusive and are intended to ensure better security for users. However, in this case the changes published in July of this year (and set to take effect in November 2015) will probably break a significant number of corporate networks simply because the changes are in direct opposition to the best practices that Microsoft and many others have been recommending for years. This is the practice of separating internal and external domain names for security and identification. The CA/Browser Forum announced back in July that they are going to put an end to this practice by November 2015.
Microsoft's UEFI Secure Boot Locking Out Choice and The Competition In The Name of Security
 A second Linux Distro has joined the Microsoft Secure Booth party. You see Microsoft has come up with what they are calling the UEFI Secure Boot. UEFI Secure boot is somewhat controversial in that once set up it will only allow signed versions of an OS to be installed. This means that if a computer is shipped from an OEM with Windows 8 and UEFI Secure Boot on you could not install a generic version of Linux or indeed any other OS including Windows 7 etc. This would effectively lock someone into using Windows 8 only on these devices. This block would include even downgrading your new system to Windows 7.
A second Linux Distro has joined the Microsoft Secure Booth party. You see Microsoft has come up with what they are calling the UEFI Secure Boot. UEFI Secure boot is somewhat controversial in that once set up it will only allow signed versions of an OS to be installed. This means that if a computer is shipped from an OEM with Windows 8 and UEFI Secure Boot on you could not install a generic version of Linux or indeed any other OS including Windows 7 etc. This would effectively lock someone into using Windows 8 only on these devices. This block would include even downgrading your new system to Windows 7.
A Google SSL Cert issued to... Someone that was not Google
Not that long ago Microsoft was the victim of an incorrectly assigned certificate. This was issued to more than just Microsoft and caused some havoc with a few firewalls (like Microsoft’s ISA) that check for security certificate validity. Because of the malformed Cert people were not able to get to Hotmail and other secure Microsoft sites or they received an error saying the certificate could not be trusted. Microsoft quickly remedied the issue, but it had an impact. 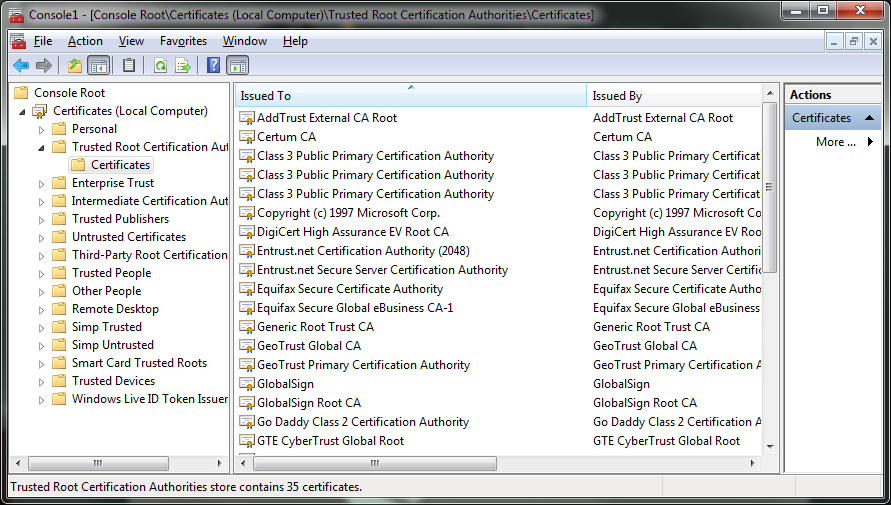 Now we see something similar has happened to Google. A Dutch certificate service by the name of DigiNotar issued a certificate for Google.com to a company that is certainly not Google. The response has been immediate with companies stating that they are going to release patches that will revoke the DigiNotar trust (which is not found in many US systems but is big in Europe apparently.
Now we see something similar has happened to Google. A Dutch certificate service by the name of DigiNotar issued a certificate for Google.com to a company that is certainly not Google. The response has been immediate with companies stating that they are going to release patches that will revoke the DigiNotar trust (which is not found in many US systems but is big in Europe apparently.
Some are attributing this attack to the Iranian Government or others inside Iran. This is mostly due to the Comodo issue that happened a few months ago that was claimed by an Iranian Patriot. However, there is no evidence that this was the case this time this could be the work of others, but it does illustrate a fundamental flaw with Security Certificates. You see as it stands right now a third party is responsible for verification and issuance of the certificate that proves that a website is how it claims it is. It is not all that hard to intercept the confirmation notices in reality. It is also possible that some companies (there are well over 600 Certificate Authorities now) are unscrupulous enough that they might sell off the master keys to a site so that someone could produce their own certificates.
In short there needs to be a serious overhaul of this system to protect against the increasingly sophisticated attacks that are happening on the web.
Discuss in our Forum
