From The Blog
-
ConnectWise Slash and Grab Flaw Once Again Shows the Value of Input Validation We talk to Huntress About its Impact
Written by Sean KalinichAlthough the news of the infamous ConnectWise flaw which allowed for the creation of admin accounts is a bit cold, it still is one that…Written on Tuesday, 19 March 2024 12:44 in Security Talk Read 680 times Read more...
-
Social Manipulation as a Service – When the Bots on Twitter get their Check marks
Written by Sean KalinichWhen I started DecryptedTech it was to counter all the crap marketing I saw from component makers. I wanted to prove people with a clean…Written on Monday, 04 March 2024 16:17 in Editorials Read 1566 times Read more...
-
To Release or not to Release a PoC or OST That is the Question
Written by Sean KalinichThere is (and always has been) a debate about the ethics and impact of the release of Proof-of-Concept Exploit for an identified vulnerability and Open-Source…Written on Monday, 26 February 2024 13:05 in Security Talk Read 1100 times Read more...
-
There was an Important Lesson Learned in the LockBit Takedown and it was Not About Threat Groups
Written by Sean KalinichIn what could be called a fantastic move, global law enforcement agencies attacked and took down LockBit’s infrastructure. The day of the event was filled…Written on Thursday, 22 February 2024 12:20 in Security Talk Read 1069 times Read more...
-
NetSPI’s Offensive Security Offering Leverages Subject Matter Experts to Enhance Pen Testing
Written by Sean KalinichBlack Hat 2023 Las Vegas. The term offensive security has always been an interesting one for me. On the surface is brings to mind reaching…Written on Tuesday, 12 September 2023 17:05 in Security Talk Read 2120 times Read more...
-
Black Kite Looks to Offer a Better View of Risk in a Rapidly Changing Threat Landscape
Written by Sean KalinichBlack Hat 2023 – Las Vegas. Risk is an interesting subject and has many different meanings to many different people. For the most part Risk…Written on Tuesday, 12 September 2023 14:56 in Security Talk Read 1838 times Read more...
-
Microsoft Finally Reveals how they Believe a Consumer Signing Key was Stollen
Written by Sean KalinichIn May of 2023 a few sensitive accounts reported to Microsoft that their environments appeared to be compromised. Due to the nature of these accounts,…Written on Thursday, 07 September 2023 14:40 in Security Talk Read 2110 times Read more...
-
Mandiant Releases a Detailed Look at the Campaign Targeting Barracuda Email Security Gateways, I Take a Look at What this all Might Mean
Written by Sean KalinichThe recent attack that leveraged a 0-Day vulnerability to compromise a number of Barracuda Email Security Gateway appliances (physical and virtual, but not cloud) was…Written on Wednesday, 30 August 2023 16:09 in Security Talk Read 2088 times Read more...
-
Threat Groups Return to Targeting Developers in Recent Software Supply Chain Attacks
Written by Sean KalinichThere is a topic of conversation that really needs to be talked about in the open. It is the danger of developer systems (personal and…Written on Wednesday, 30 August 2023 13:29 in Security Talk Read 1876 times Read more...
Recent Comments
- Sean, this is a fantastic review of a beautiful game. I do agree with you… Written by Jacob 2023-05-19 14:17:50 Jedi Survivor – The Quick, Dirty, and Limited Spoilers Review
- Great post. Very interesting read but is the reality we are currently facing. Written by JP 2023-05-03 02:33:53 The Dangers of AI; I Think I Have Seen this Movie Before
- I was wondering if you have tested the microphone audio frequency for the Asus HS-1000W? Written by Maciej 2020-12-18 14:09:33 Asus HS-1000W wireless headset impresses us in the lab
- Thanks for review. I appreciate hearing from a real pro as opposed to the blogger… Written by Keith 2019-06-18 04:22:36 The Red Hydrogen One, Possibly One of the Most “misunderstood” Phones Out
- Have yet to see the real impact but in the consumer segment, ryzen series are… Written by sushant 2018-12-23 10:12:12 AMD’s 11-year journey to relevance gets an epic finish.
Most Read
- Microsoft Fail - Start Button Back in Windows 8.1 But No Start Menu Written on Thursday, 30 May 2013 15:33 in News Be the first to comment! Read 116514 times Read more...
- We take a look at the NETGEAR ProSafe WNDAP360 Dual-Band Wireless Access Point Written on Saturday, 07 April 2012 00:17 in Pro Storage and Networking Be the first to comment! Read 87450 times Read more...
- Synology DS1512+ Five-Bay NAS Performance Review Written on Tuesday, 12 June 2012 20:31 in Pro Storage and Networking Be the first to comment! Read 81994 times Read more...
- Gigabyte G1.Sniper M3 Design And Feature Review Written on Sunday, 19 August 2012 22:35 in Enthusiast Motherboards Be the first to comment! Read 80308 times Read more...
- The Asus P8Z77-M Pro Brings Exceptional Performance and Value to the Lab Written on Monday, 23 April 2012 13:02 in Consumer Motherboards Be the first to comment! Read 70962 times Read more...
Displaying items by tag: Stuxnet
US/Israel Flame Collaboration Rumor Misses Some Facts and Almost Looks Too Well Timed To be True
 There are two things about leaks that always concern me; the content of the leak, who it was leaked to, and … (Ok three things I look at when dealing with leaks) the timing. Now when the leak hit concerning Stuxnet and Duqu we took a look at the information and compared it with some information we were able to dig up including the timing of the attack and a few other factors. The leak seemed to fit the facts. At the time of the leak there was no mention of Flame, any program to gather intelligence, or even hints that there might be more out there.
There are two things about leaks that always concern me; the content of the leak, who it was leaked to, and … (Ok three things I look at when dealing with leaks) the timing. Now when the leak hit concerning Stuxnet and Duqu we took a look at the information and compared it with some information we were able to dig up including the timing of the attack and a few other factors. The leak seemed to fit the facts. At the time of the leak there was no mention of Flame, any program to gather intelligence, or even hints that there might be more out there.
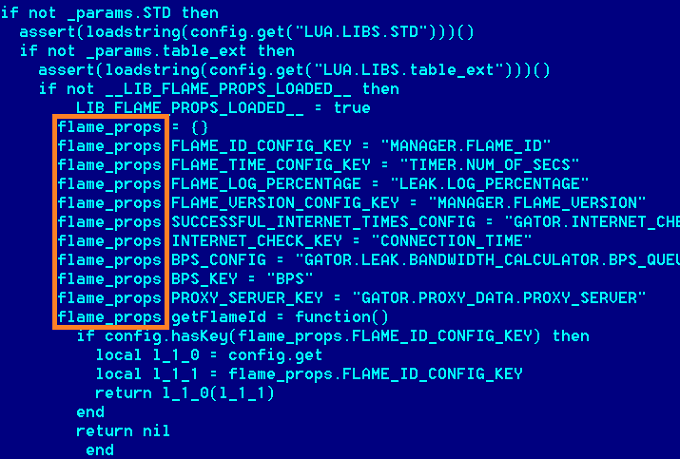
Flame and Stuxnet Devs Appear to Have Shared Source Code At Least Once
 It would appear that the developers of Stuxnet/Duqu and Flame shared at least some source code during development. At least that is what security research firm Kaspersky seems to think. Kaspersky was the company that found the massive bit of malware that was using a compromised Microsoft Terminal Server licensing model to sign certificates for their code. Flame appears to have been a very coordinated espionage attack on Iran and has been in the news thanks to the complexity and functionality that it has.
It would appear that the developers of Stuxnet/Duqu and Flame shared at least some source code during development. At least that is what security research firm Kaspersky seems to think. Kaspersky was the company that found the massive bit of malware that was using a compromised Microsoft Terminal Server licensing model to sign certificates for their code. Flame appears to have been a very coordinated espionage attack on Iran and has been in the news thanks to the complexity and functionality that it has.
Stuxnet Was A US Operation... Now the push for SOPA, PIPA and CISPA by Congress Makes a Little More Sense...
 In every occasion if you dig deep enough you will find the reasons for someone’s actions, even if they seem completely random. For a while now we have watched as congress has pushed one stupid internet control law after another. For many (us included) we have felt that this was at the request of the MPAA, RIAA and other copyright holders. After all the measures and consequences in the laws were geared toward them and helping them to “prevent piracy”.
In every occasion if you dig deep enough you will find the reasons for someone’s actions, even if they seem completely random. For a while now we have watched as congress has pushed one stupid internet control law after another. For many (us included) we have felt that this was at the request of the MPAA, RIAA and other copyright holders. After all the measures and consequences in the laws were geared toward them and helping them to “prevent piracy”.
Massive "Flame" Cyber Attack Targeted At Some Middle Eastern Countries
 An interesting report has popped up about a rather large attack on a group of Middle Eastern countries. The attack (called Flame) appears to be a targeted attack against Iran, Israel, Palestine, Sudan, Syria, Lebanon, Saudi Arabia and Egypt with the most effected being Iran, Palestine, and Israel. The attack was reported by Kaspersky Labs and looks to be intended to collect all kinds of information (not just data on computers). Kaspersky believes that Flame has been operating for at least two years in this region.
An interesting report has popped up about a rather large attack on a group of Middle Eastern countries. The attack (called Flame) appears to be a targeted attack against Iran, Israel, Palestine, Sudan, Syria, Lebanon, Saudi Arabia and Egypt with the most effected being Iran, Palestine, and Israel. The attack was reported by Kaspersky Labs and looks to be intended to collect all kinds of information (not just data on computers). Kaspersky believes that Flame has been operating for at least two years in this region.
SCADA Vulnerability used in Illinois water plant breach
 Remember when we told you about the SCADA vulnerabilities (here and here)? Well back in August we talked at length about how many of these control systems not only use the default passwords but are connected to the internet. On top of all of these there are a large number that have no high-level security (beyond simple passwords). This puts many of our vital infrastructure services at great risk to compromise from outside parties.
Remember when we told you about the SCADA vulnerabilities (here and here)? Well back in August we talked at length about how many of these control systems not only use the default passwords but are connected to the internet. On top of all of these there are a large number that have no high-level security (beyond simple passwords). This puts many of our vital infrastructure services at great risk to compromise from outside parties.
New Malware Found with Stuxnet Similarities
 Just in case all of the warnings that we gave you before about SCDA (Supervisory Control and Data Acquisition) devices and how insecure most of them are was not enough. We now find that a new piece of malware that appears to be intended spy on industrial networks as a precursor to a future attack like the Stuxnet malware that hit last year. Dubbed Duqu because of a prefix attached to files the new malware creates this new bit of code is very concerning to security experts.
Just in case all of the warnings that we gave you before about SCDA (Supervisory Control and Data Acquisition) devices and how insecure most of them are was not enough. We now find that a new piece of malware that appears to be intended spy on industrial networks as a precursor to a future attack like the Stuxnet malware that hit last year. Dubbed Duqu because of a prefix attached to files the new malware creates this new bit of code is very concerning to security experts.
The code was found on several Windows based systems across multiple companies in Europe. These companies were not directly identified but all appear to have connections to industries that directly interact with basic infrastructure services. As of right now Duqu appears content to just gather information and report back to its command and control servers (including using an internal key logger). Duqu also appears to be sending JPG files back and forth between the server and the infected system, but as many found out to their dismay you can embed quite a bit of information in a JPG files so these could be used to send control instructions and responses or could be nothing more than test files right now.
So far researchers are at a loss as to what Duqu is collecting and why this is happening. They do know that the attacks have been going on since at least December 2010 and that the first variant identified used a stolen certificate much like the original Stuxnet did. Researchers at Symantec and McAfee also feel that the creators of this code had access to the source code of Stuxnet as the two pieces of Malware are very similar in the way they operate and the coding used. Both McAfee and Symantec have also stated that Duqu does not spread and that it does not appear to use any known exploits. This would indicate that the malware uses tactics like drive-by, or social engineering based exploits. These rely on human intervention to download and install the malicious code on a system usually via email or web link.
We personally wonder if this is related to some of the rumors about Anonymous stepping up their attacks on Governments and Large Corporations. After all with what they can gather using some fairly simple techniques (and a nice bit of coding) they can put some rather devastating plans into action very quickly. If this is the case (and this is all just speculation) then we might be looking at an attack that no one is really prepared for. Then again this could all be nothing more than a reconnaissance mission, especially considering the fact that the code uninstalls itself after 30 days…
Source Symantec and McAfee
Discuss this in our Forum
