From The Blog
-
ConnectWise Slash and Grab Flaw Once Again Shows the Value of Input Validation We talk to Huntress About its Impact
Written by Sean KalinichAlthough the news of the infamous ConnectWise flaw which allowed for the creation of admin accounts is a bit cold, it still is one that…Written on Tuesday, 19 March 2024 12:44 in Security Talk Read 710 times Read more...
-
Social Manipulation as a Service – When the Bots on Twitter get their Check marks
Written by Sean KalinichWhen I started DecryptedTech it was to counter all the crap marketing I saw from component makers. I wanted to prove people with a clean…Written on Monday, 04 March 2024 16:17 in Editorials Read 1587 times Read more...
-
To Release or not to Release a PoC or OST That is the Question
Written by Sean KalinichThere is (and always has been) a debate about the ethics and impact of the release of Proof-of-Concept Exploit for an identified vulnerability and Open-Source…Written on Monday, 26 February 2024 13:05 in Security Talk Read 1120 times Read more...
-
There was an Important Lesson Learned in the LockBit Takedown and it was Not About Threat Groups
Written by Sean KalinichIn what could be called a fantastic move, global law enforcement agencies attacked and took down LockBit’s infrastructure. The day of the event was filled…Written on Thursday, 22 February 2024 12:20 in Security Talk Read 1095 times Read more...
-
NetSPI’s Offensive Security Offering Leverages Subject Matter Experts to Enhance Pen Testing
Written by Sean KalinichBlack Hat 2023 Las Vegas. The term offensive security has always been an interesting one for me. On the surface is brings to mind reaching…Written on Tuesday, 12 September 2023 17:05 in Security Talk Read 2138 times Read more...
-
Black Kite Looks to Offer a Better View of Risk in a Rapidly Changing Threat Landscape
Written by Sean KalinichBlack Hat 2023 – Las Vegas. Risk is an interesting subject and has many different meanings to many different people. For the most part Risk…Written on Tuesday, 12 September 2023 14:56 in Security Talk Read 1863 times Read more...
-
Microsoft Finally Reveals how they Believe a Consumer Signing Key was Stollen
Written by Sean KalinichIn May of 2023 a few sensitive accounts reported to Microsoft that their environments appeared to be compromised. Due to the nature of these accounts,…Written on Thursday, 07 September 2023 14:40 in Security Talk Read 2136 times Read more...
-
Mandiant Releases a Detailed Look at the Campaign Targeting Barracuda Email Security Gateways, I Take a Look at What this all Might Mean
Written by Sean KalinichThe recent attack that leveraged a 0-Day vulnerability to compromise a number of Barracuda Email Security Gateway appliances (physical and virtual, but not cloud) was…Written on Wednesday, 30 August 2023 16:09 in Security Talk Read 2105 times Read more...
-
Threat Groups Return to Targeting Developers in Recent Software Supply Chain Attacks
Written by Sean KalinichThere is a topic of conversation that really needs to be talked about in the open. It is the danger of developer systems (personal and…Written on Wednesday, 30 August 2023 13:29 in Security Talk Read 1899 times Read more...
Recent Comments
- Sean, this is a fantastic review of a beautiful game. I do agree with you… Written by Jacob 2023-05-19 14:17:50 Jedi Survivor – The Quick, Dirty, and Limited Spoilers Review
- Great post. Very interesting read but is the reality we are currently facing. Written by JP 2023-05-03 02:33:53 The Dangers of AI; I Think I Have Seen this Movie Before
- I was wondering if you have tested the microphone audio frequency for the Asus HS-1000W? Written by Maciej 2020-12-18 14:09:33 Asus HS-1000W wireless headset impresses us in the lab
- Thanks for review. I appreciate hearing from a real pro as opposed to the blogger… Written by Keith 2019-06-18 04:22:36 The Red Hydrogen One, Possibly One of the Most “misunderstood” Phones Out
- Have yet to see the real impact but in the consumer segment, ryzen series are… Written by sushant 2018-12-23 10:12:12 AMD’s 11-year journey to relevance gets an epic finish.
Most Read
- Microsoft Fail - Start Button Back in Windows 8.1 But No Start Menu Written on Thursday, 30 May 2013 15:33 in News Be the first to comment! Read 116533 times Read more...
- We take a look at the NETGEAR ProSafe WNDAP360 Dual-Band Wireless Access Point Written on Saturday, 07 April 2012 00:17 in Pro Storage and Networking Be the first to comment! Read 87508 times Read more...
- Synology DS1512+ Five-Bay NAS Performance Review Written on Tuesday, 12 June 2012 20:31 in Pro Storage and Networking Be the first to comment! Read 82051 times Read more...
- Gigabyte G1.Sniper M3 Design And Feature Review Written on Sunday, 19 August 2012 22:35 in Enthusiast Motherboards Be the first to comment! Read 80343 times Read more...
- The Asus P8Z77-M Pro Brings Exceptional Performance and Value to the Lab Written on Monday, 23 April 2012 13:02 in Consumer Motherboards Be the first to comment! Read 71005 times Read more...
Displaying items by tag: Certificate
Rouge Access Points Can Be Used to Exploit Flaw In PEAP-MSCHAPv2 on Mobile Devices
 |
Microsoft has had its share of flaws to deal with over a wide range of products. So it is no surprise when we read that there is another “flaw” making the rounds that is related to an older flaw that someone exposed about a year ago. The first flaw was a laughable encryption scheme that was intended to protect the username and password when using PEAP-MSCHAPv2 authentication. In this flaw someone was able to quickly break the encryption and access the credentials used to log on. This flaw does require access to the device that the user was connecting to (RAIDUS server, Firewall, etc.) so it is a little harder to pull off. Now it looks like there is a further flaw that will remove the need to compromise other equipment.
Flame Was Using Subverted Microsoft Certificates To Infect Systems; Microsoft Issues a Patch to Correct This.
 We told you about the new malware threat in Iran (and some other Middle Eastern countries). This is a new and very sophisticated bit of spyware that appears designed to gather intelligence about the state of Iran’s nuclear program. Kaspersky discovered the worm after being asked to check some systems that appeared to be acting strange. This investigation led to the discovery on Flame and the identification of some 20 plug-ins for the malware that can do everything from capture screens, to turning on a system’s microphone to record anything around the system. It is also able to record VoIP communication through applications like Skype.
We told you about the new malware threat in Iran (and some other Middle Eastern countries). This is a new and very sophisticated bit of spyware that appears designed to gather intelligence about the state of Iran’s nuclear program. Kaspersky discovered the worm after being asked to check some systems that appeared to be acting strange. This investigation led to the discovery on Flame and the identification of some 20 plug-ins for the malware that can do everything from capture screens, to turning on a system’s microphone to record anything around the system. It is also able to record VoIP communication through applications like Skype.
A Google SSL Cert issued to... Someone that was not Google
Not that long ago Microsoft was the victim of an incorrectly assigned certificate. This was issued to more than just Microsoft and caused some havoc with a few firewalls (like Microsoft’s ISA) that check for security certificate validity. Because of the malformed Cert people were not able to get to Hotmail and other secure Microsoft sites or they received an error saying the certificate could not be trusted. Microsoft quickly remedied the issue, but it had an impact. 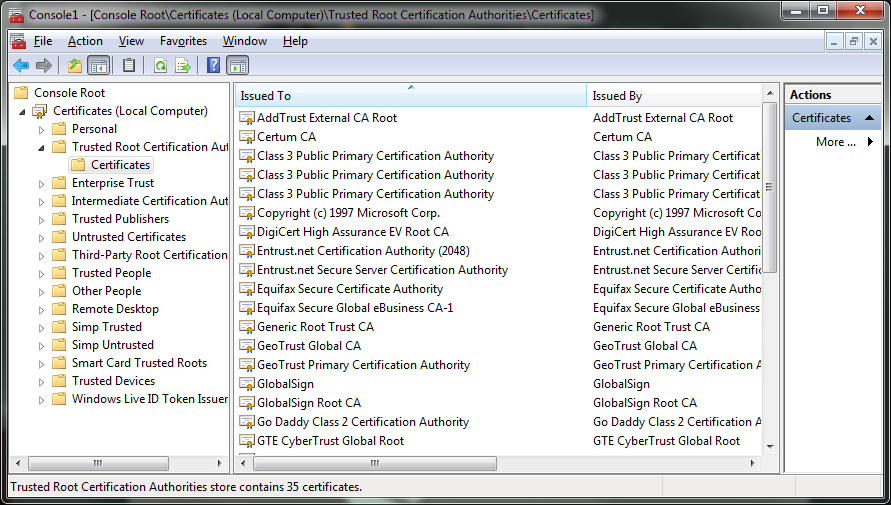 Now we see something similar has happened to Google. A Dutch certificate service by the name of DigiNotar issued a certificate for Google.com to a company that is certainly not Google. The response has been immediate with companies stating that they are going to release patches that will revoke the DigiNotar trust (which is not found in many US systems but is big in Europe apparently.
Now we see something similar has happened to Google. A Dutch certificate service by the name of DigiNotar issued a certificate for Google.com to a company that is certainly not Google. The response has been immediate with companies stating that they are going to release patches that will revoke the DigiNotar trust (which is not found in many US systems but is big in Europe apparently.
Some are attributing this attack to the Iranian Government or others inside Iran. This is mostly due to the Comodo issue that happened a few months ago that was claimed by an Iranian Patriot. However, there is no evidence that this was the case this time this could be the work of others, but it does illustrate a fundamental flaw with Security Certificates. You see as it stands right now a third party is responsible for verification and issuance of the certificate that proves that a website is how it claims it is. It is not all that hard to intercept the confirmation notices in reality. It is also possible that some companies (there are well over 600 Certificate Authorities now) are unscrupulous enough that they might sell off the master keys to a site so that someone could produce their own certificates.
In short there needs to be a serious overhaul of this system to protect against the increasingly sophisticated attacks that are happening on the web.
Discuss in our Forum
