From The Blog
-
ConnectWise Slash and Grab Flaw Once Again Shows the Value of Input Validation We talk to Huntress About its Impact
Written by Sean KalinichAlthough the news of the infamous ConnectWise flaw which allowed for the creation of admin accounts is a bit cold, it still is one that…Written on Tuesday, 19 March 2024 12:44 in Security Talk Read 702 times Read more...
-
Social Manipulation as a Service – When the Bots on Twitter get their Check marks
Written by Sean KalinichWhen I started DecryptedTech it was to counter all the crap marketing I saw from component makers. I wanted to prove people with a clean…Written on Monday, 04 March 2024 16:17 in Editorials Read 1577 times Read more...
-
To Release or not to Release a PoC or OST That is the Question
Written by Sean KalinichThere is (and always has been) a debate about the ethics and impact of the release of Proof-of-Concept Exploit for an identified vulnerability and Open-Source…Written on Monday, 26 February 2024 13:05 in Security Talk Read 1113 times Read more...
-
There was an Important Lesson Learned in the LockBit Takedown and it was Not About Threat Groups
Written by Sean KalinichIn what could be called a fantastic move, global law enforcement agencies attacked and took down LockBit’s infrastructure. The day of the event was filled…Written on Thursday, 22 February 2024 12:20 in Security Talk Read 1085 times Read more...
-
NetSPI’s Offensive Security Offering Leverages Subject Matter Experts to Enhance Pen Testing
Written by Sean KalinichBlack Hat 2023 Las Vegas. The term offensive security has always been an interesting one for me. On the surface is brings to mind reaching…Written on Tuesday, 12 September 2023 17:05 in Security Talk Read 2133 times Read more...
-
Black Kite Looks to Offer a Better View of Risk in a Rapidly Changing Threat Landscape
Written by Sean KalinichBlack Hat 2023 – Las Vegas. Risk is an interesting subject and has many different meanings to many different people. For the most part Risk…Written on Tuesday, 12 September 2023 14:56 in Security Talk Read 1856 times Read more...
-
Microsoft Finally Reveals how they Believe a Consumer Signing Key was Stollen
Written by Sean KalinichIn May of 2023 a few sensitive accounts reported to Microsoft that their environments appeared to be compromised. Due to the nature of these accounts,…Written on Thursday, 07 September 2023 14:40 in Security Talk Read 2124 times Read more...
-
Mandiant Releases a Detailed Look at the Campaign Targeting Barracuda Email Security Gateways, I Take a Look at What this all Might Mean
Written by Sean KalinichThe recent attack that leveraged a 0-Day vulnerability to compromise a number of Barracuda Email Security Gateway appliances (physical and virtual, but not cloud) was…Written on Wednesday, 30 August 2023 16:09 in Security Talk Read 2098 times Read more...
-
Threat Groups Return to Targeting Developers in Recent Software Supply Chain Attacks
Written by Sean KalinichThere is a topic of conversation that really needs to be talked about in the open. It is the danger of developer systems (personal and…Written on Wednesday, 30 August 2023 13:29 in Security Talk Read 1893 times Read more...
Recent Comments
- Sean, this is a fantastic review of a beautiful game. I do agree with you… Written by Jacob 2023-05-19 14:17:50 Jedi Survivor – The Quick, Dirty, and Limited Spoilers Review
- Great post. Very interesting read but is the reality we are currently facing. Written by JP 2023-05-03 02:33:53 The Dangers of AI; I Think I Have Seen this Movie Before
- I was wondering if you have tested the microphone audio frequency for the Asus HS-1000W? Written by Maciej 2020-12-18 14:09:33 Asus HS-1000W wireless headset impresses us in the lab
- Thanks for review. I appreciate hearing from a real pro as opposed to the blogger… Written by Keith 2019-06-18 04:22:36 The Red Hydrogen One, Possibly One of the Most “misunderstood” Phones Out
- Have yet to see the real impact but in the consumer segment, ryzen series are… Written by sushant 2018-12-23 10:12:12 AMD’s 11-year journey to relevance gets an epic finish.
Most Read
- Microsoft Fail - Start Button Back in Windows 8.1 But No Start Menu Written on Thursday, 30 May 2013 15:33 in News Be the first to comment! Read 116526 times Read more...
- We take a look at the NETGEAR ProSafe WNDAP360 Dual-Band Wireless Access Point Written on Saturday, 07 April 2012 00:17 in Pro Storage and Networking Be the first to comment! Read 87481 times Read more...
- Synology DS1512+ Five-Bay NAS Performance Review Written on Tuesday, 12 June 2012 20:31 in Pro Storage and Networking Be the first to comment! Read 82031 times Read more...
- Gigabyte G1.Sniper M3 Design And Feature Review Written on Sunday, 19 August 2012 22:35 in Enthusiast Motherboards Be the first to comment! Read 80336 times Read more...
- The Asus P8Z77-M Pro Brings Exceptional Performance and Value to the Lab Written on Monday, 23 April 2012 13:02 in Consumer Motherboards Be the first to comment! Read 70988 times Read more...
Displaying items by tag: Intellectual Property
Did Apple copy the Swiss Federal Railways clock?
 |
Apple, the big company that likes to brag about their “originality” and accuse everybody else of stealing their ideas, apparently stole something from Switzerland. This is the country famous for inventing clocks and watches, and not just any kind of it, but truly of the highest quality and with beautiful design. Now, the Swiss Federal Railways have accused Apple that of copying their official railway clock.
ACTA Is Getting More Serious Oposition in the US and in the EU
 ACTA is in the news again today as we hear from more than a few people on the implications of the treaty and what consequences it might have. Interestingly it looks like ACTA was originally designed to handle the large scale manufacture and distribution of counterfeit physical products (for prescription drugs actually). Some have suggested that the import of items (like the fake Gucci and Fendi bags you can find for sale on some street corners…) has a drastic impact on the sales and profit of those companies. This is the same logic that is put forward for the theft of virtual property like IP, music, and videos.
ACTA is in the news again today as we hear from more than a few people on the implications of the treaty and what consequences it might have. Interestingly it looks like ACTA was originally designed to handle the large scale manufacture and distribution of counterfeit physical products (for prescription drugs actually). Some have suggested that the import of items (like the fake Gucci and Fendi bags you can find for sale on some street corners…) has a drastic impact on the sales and profit of those companies. This is the same logic that is put forward for the theft of virtual property like IP, music, and videos.
What If All of the Java APIs were not free? How Many Applications Could no Longer Be Sold?
 In another installment of our “and that is why you fail” byline we come to the small dispute between Google and Oracle. On the table is not if Google use Java APIs or not, but the basic question of “are Java APIs free to use for development?” This issue is a huge one as a Google loss could set precedent for Oracle to go after ANYONE that is using the Java API without paying royalties to Oracle for their use.
In another installment of our “and that is why you fail” byline we come to the small dispute between Google and Oracle. On the table is not if Google use Java APIs or not, but the basic question of “are Java APIs free to use for development?” This issue is a huge one as a Google loss could set precedent for Oracle to go after ANYONE that is using the Java API without paying royalties to Oracle for their use.
Judge Says; You Cannot Steal Code...
 A recent decision in an appeals court could have disastrous effects on Intellectual Property rights holders in the US and possibly around the globe. Not all that long ago a software developer grabbed a chunk of code from Goldman Sachs as he was on his way out of the door. The code related to a high=speed trading application that Goldman Sachs uses for business. The firm immediately went after the programmer (Sergey Aleynikov) and he was convicted under the National Stolen Property Act.
A recent decision in an appeals court could have disastrous effects on Intellectual Property rights holders in the US and possibly around the globe. Not all that long ago a software developer grabbed a chunk of code from Goldman Sachs as he was on his way out of the door. The code related to a high=speed trading application that Goldman Sachs uses for business. The firm immediately went after the programmer (Sergey Aleynikov) and he was convicted under the National Stolen Property Act.
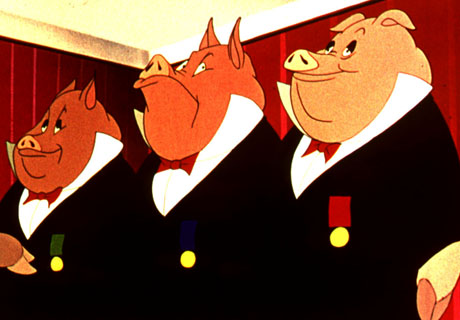
Bad Cybersecurity Laws All Boil Down To Ignorance and Greed
 We have always been a supporter of certain Internet freedoms as well as individual privacy (no surprise there huh). Bills like PIPA and SOPA showed us a glaring issue with the existing level of knowledge currently held by the people that make our laws (and not just in the US). This is not a big shocker to most people either. It is fairly common knowledge that our law makers get into office based on little more than a popularity contest that is held every few years. Once in office they are like the gullible kid in school that gets talked into things, by the “cool kids”, but in this case the cool kids are lobbyists and are not looking for a laugh they are looking to improve their control and profit.
We have always been a supporter of certain Internet freedoms as well as individual privacy (no surprise there huh). Bills like PIPA and SOPA showed us a glaring issue with the existing level of knowledge currently held by the people that make our laws (and not just in the US). This is not a big shocker to most people either. It is fairly common knowledge that our law makers get into office based on little more than a popularity contest that is held every few years. Once in office they are like the gullible kid in school that gets talked into things, by the “cool kids”, but in this case the cool kids are lobbyists and are not looking for a laugh they are looking to improve their control and profit.
The Internet Faces Serious Growing Pains as it Matures, But it Will Survive Even the Most Restrictive Law
 Today is a busy day on the Internet (it usually is on a Monday morning). There are multiple articles and comments that are all related to the freedom of the Internet and how the world is evolving to embrace it while some in power are de-evolving to tray and restrict it. At this point there is no clear winner, but the sides are being firmly drawn in the sand and it is clear that things will get worse before they get better.
Today is a busy day on the Internet (it usually is on a Monday morning). There are multiple articles and comments that are all related to the freedom of the Internet and how the world is evolving to embrace it while some in power are de-evolving to tray and restrict it. At this point there is no clear winner, but the sides are being firmly drawn in the sand and it is clear that things will get worse before they get better.
ACTA and other "Trade Agreements" seek to bypass laws and violate civil rights.
 After both SOPA and PIPA were publicly shelved the US government did what it always does. It finds a way to do what it wants, but by hiding it in other bills or (as is becoming more common) using trade agreements to by-pass laws altogether. This is exactly what we are seeing with ACTA and TPP. These two trade agreements are probably some of the most dangerous bits of work that we have read about in a very long time.
After both SOPA and PIPA were publicly shelved the US government did what it always does. It finds a way to do what it wants, but by hiding it in other bills or (as is becoming more common) using trade agreements to by-pass laws altogether. This is exactly what we are seeing with ACTA and TPP. These two trade agreements are probably some of the most dangerous bits of work that we have read about in a very long time.
